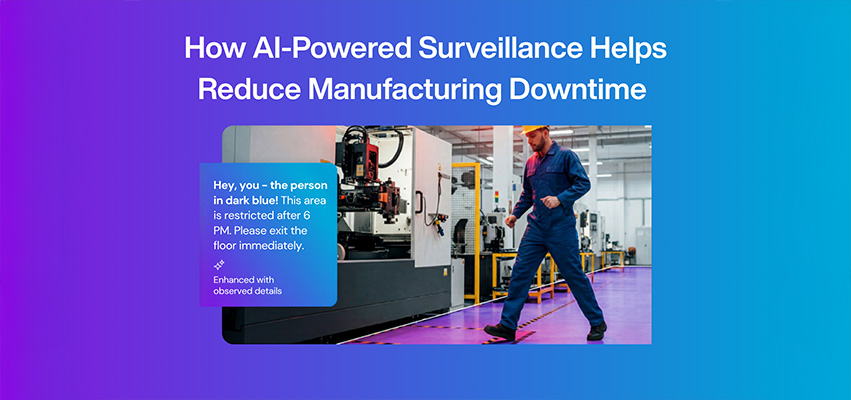
Unplanned downtime in manufacturing does not always start with equipment failure. In many cases, it begins with unauthorized access, unsafe behavior, restricted-area violations, or delayed incident response. Modern manufacturing facilities are increasingly adopting AI-powered surveillance systems to improve safety, reduce operational…
How AI-Powered Surveillance with Verkada is Transforming Job Site Security
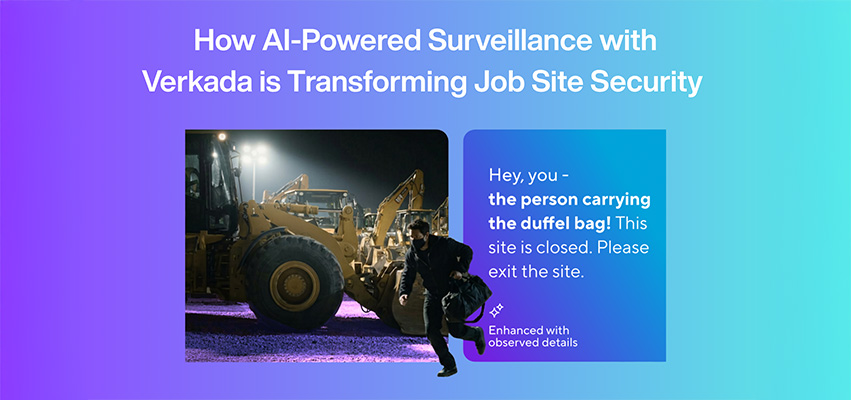
Site theft doesn’t start with a break-in. It starts with opportunity. Construction sites, commercial developments, and industrial environments are highly vulnerable to theft, vandalism, and unauthorized access. Traditional security systems are often reactive, capturing incidents after they happen rather than preventing…
Cloud-Based Intercom Systems: Why Organizations Are Moving to Verkada Intercom
Modern organizations expect more from building entry systems. Traditional intercoms often operate as standalone devices, offering limited visibility, manual workflows, and minimal integration with broader security infrastructure. Cloud-based intercom systems like Verkada are helping organizations modernize entry management by combining video…
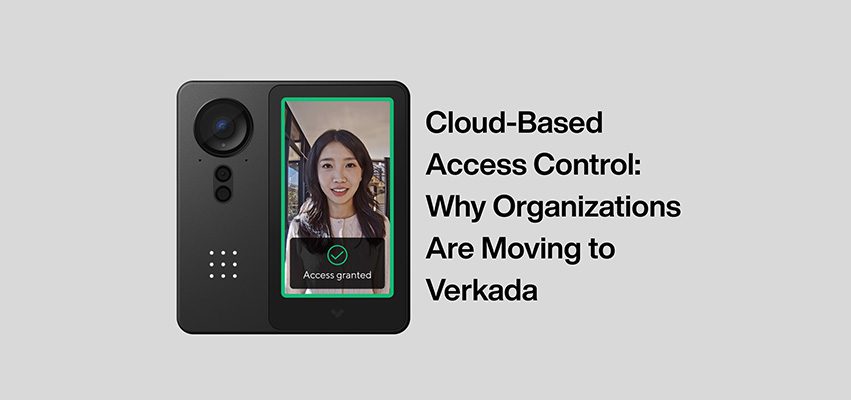
Cloud-Based Access Control: Why Organizations Are Moving to Verkada
Traditional access control systems often rely on on-premise servers, manual updates, and complex infrastructure. These systems can be difficult to scale, especially for organizations managing multiple locations. Cloud-based access control simplifies deployment and management. With Verkada Access Control, organizations can deploy…
Intelligent PTZ Security Cameras: How Verkada Improves Large-Area Surveillance
Modern security environments often extend far beyond traditional indoor spaces. Organizations must monitor large areas such as parking lots, campuses, distribution centers, and building entrances while maintaining clear visibility and fast response capabilities. Fixed security cameras provide consistent coverage, but large…
How AI-Powered Video Platforms Are Transforming Enterprise Security Operations
Enterprise security leaders face a growing challenge. Cameras are everywhere, but finding the right footage quickly is often difficult. Most traditional surveillance systems simply record video to local network video recorders (NVRs). When an incident occurs, security teams must manually search…
Verkada Intercom Live Translation: AI-Powered Multilingual Entry Communication for Enterprise Security
Verkada has introduced live translation capabilities within its intercom platform, enabling real-time, two-way voice and text translation between visitors and receivers at entry points. For enterprise organizations, communication speed at the door directly impacts both security posture and visitor experience. This…
Enterprise AV Integration and Cloud-Managed Physical Security Case Studies Across Canada
GAV MGMT has launched a new Case Studies library documenting real enterprise audio visual integration and AI-enabled physical security deployments across Canada. This section provides detailed examples of how complex corporate environments are designed, standardized, integrated, and deployed at scale across…
5 Enterprise Technology Integration Trends Shaping AV and Physical Security in 2026
As organizations rethink how their spaces connect, protect, and scale, enterprise technology integration is moving beyond individual systems toward fully integrated environments. In 2026, success is defined by how intelligently AV and physical security platforms work together. Here are five technology…
Retail Loss Prevention and Security Operations: How Unified Cloud Security Helps Reduce Theft and Improve Response Time
Retail theft is not just a shrink problem. It is an operational challenge that impacts staff safety, inventory accuracy, customer experience, and profitability across every location. Many retail teams are trying to manage modern threats using outdated systems, disconnected tools, and…
Cloud Access Control Explained: Why Verkada Is the Global Leader and What It Means for Enterprise Security
Cloud access control is quickly becoming the new standard for enterprise building security. Organizations are moving away from legacy, on premise access systems in favor of modern solutions that are easier to manage, more scalable across multiple locations, and designed for…
From Reactive to Proactive: How AI-Powered Physical Security Is Changing Workplace Safety
Workplace safety is evolving, and organizations are moving away from reactive security strategies that depend on reviewing footage after something has already happened. Today, enterprise teams are adopting modern physical security systems that support proactive awareness, real-time response, and stronger operational…
Security Starts at the Door
Strong cybersecurity starts with one simple question: who has access? Every secure environment relies on control, verification, and trust. Physical access is often the first line of defense, yet it is also one of the most overlooked aspects of a cybersecurity…
Visibility Is the Foundation of Cybersecurity
Cybersecurity now extends beyond firewalls and networks. It reaches into every physical system that protects people, data, and infrastructure. The foundation of this protection is visibility. When organizations can see what is happening across every site in real time, they can…